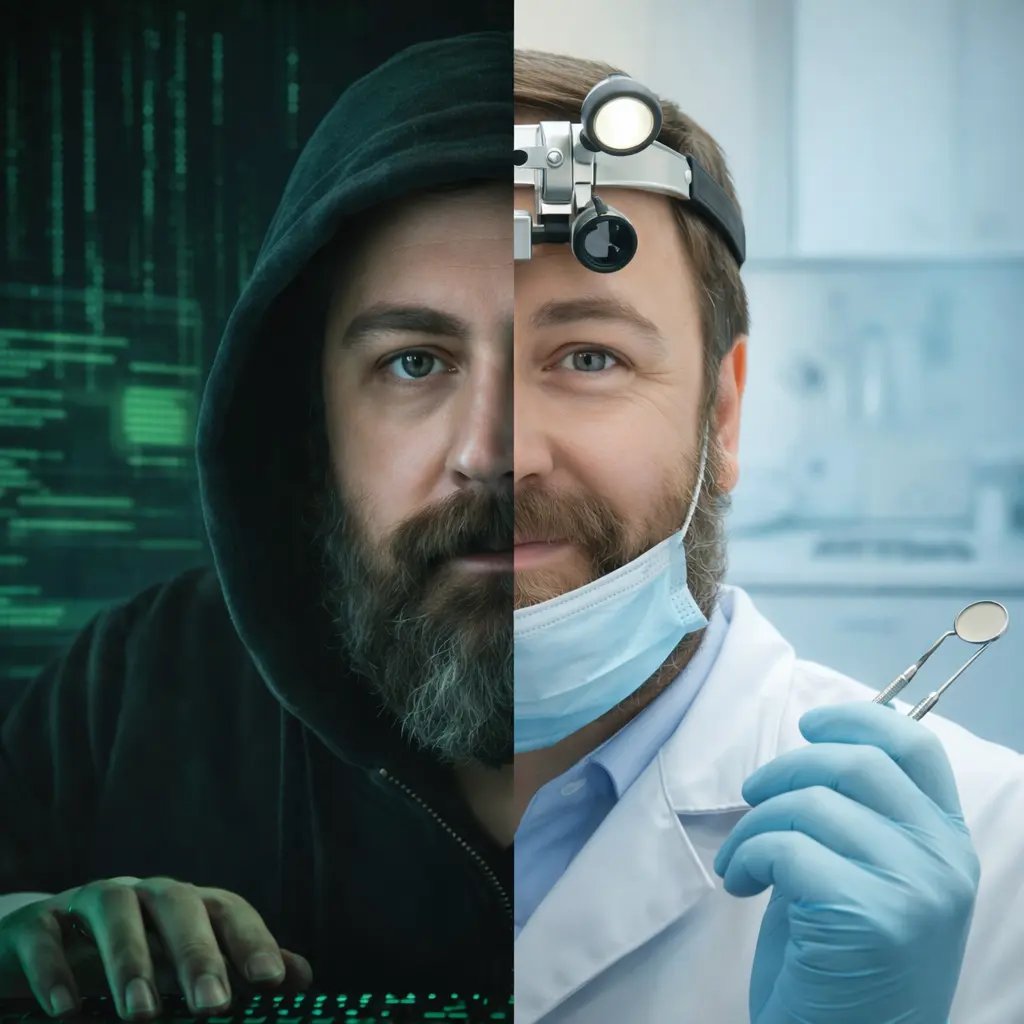
DR DAVID
SYKES
Practicing dentist. Independent cybersecurity consultant based in Durban, South Africa. 25 years in offensive security research and 13 years in clinical dentistry — operating with precision at the intersection of regulated clinical care and offensive security.